Technology-Facilitated Stalking: What You Need to Know
May 22, 2017
The Safety Net Project at the National Network to End Domestic Violence (NNEDV) explores the intersection of technology and domestic violence, stalking, sexual assault, and dating violence. Safety Net strives to help survivors increase their safety while continuing to use their technology through the provision of safety tips and tools.
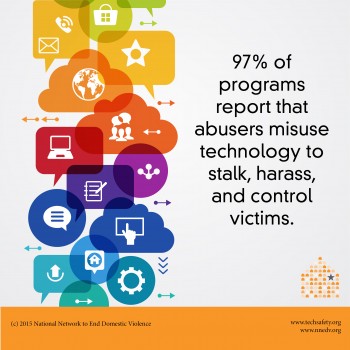
Through technology and our use of social media, we can quickly and easily connect with other people. However, typical activities such as tweeting, updating a Facebook status, or using a phone’s GPS to find local restaurants can all be misused by abusers to stalk, harass, surveil, and control victims.
“Technology doesn’t cause stalking,” said Toby Shulruff, NNEDV Senior Technology Safety Specialist, in a recent webinar hosted by Jewish Women International (JWI). “However, the integration of technology into so many aspects of our lives has made it easier for stalkers to create fear and do harm.”
What is Stalking?
Stalking is defined as a pattern of behavior directed at a specific person that would cause a reasonable person to feel fear. This pattern typically involves two or more behaviors, such as sending unwanted emails or texts or showing up at a person’s home or workplace.
The same action can hold very different meanings for different people, and what causes someone to feel fear can vary from person to person; therefore, it is important to put ourselves in the victim’s shoes.
According to the CDC, 7.5 million people are stalked in the United States each year, and women between the ages of 18 and 24 experience the highest rates of stalking.
- 61% of female victims and 44% of male victims are stalked by current or former intimate partners.
- 90% of stalking incidents are committed by someone that the victim knows.
Misusing Technology to Stalk Victims
One common form of technology-facilitated stalking is spying and eavesdropping. This is a popular method among perpetrators because it is inexpensive and easily hidden.
Mobile devices are a common target for surveillance as they have many uses. Abusers often monitor calls, texts, and voicemails, use the phone as a recording device, or track a victim’s location throughout the day.
Many other devices today have GPS built in, making it easier for victims to also be tracked through tablets, laptops, vehicle navigation systems, or location devices designed for pets, elders, and children.
Many social media apps also track a user’s location. Not only are these apps being used to track victims, but the sites are often misused to harass, defame, or impersonate a victim by creating false accounts and posting false or hurtful information. The goal of the technology abuse is often to isolate the victim from supportive friends and family, or to damage a victim’s credibility or work-life.
Preservation Considerations for Evidence Collection
When it comes to technology-facilitated abuse, preserving evidence is critical. Though our gut reaction is to hit “delete,” we need to consider documenting what’s happening on the device before removing it. There are several steps that can be taken in order to achieve this, such as:
- Coordinating with law enforcement and prosecutors early on, if you feel safe to do so.
- Keeping a stalking incident log, if possible. This helps to paint a picture for the law enforcement officer if a victim chooses to report, and it can also help to refresh a victim’s memory of the event.
- Some items to keep in the incident log include: text messages, photos, videos, voice messages, screenshots of phones and laptops, and printed emails with the header expanded.
Safety Tips for Survivors of Technology-facilitated Stalking or Abuse
Though abusers can misuse technology, it can also be used strategically by survivors to enhance or maintain safety. One of the keys is to approach safety not as a checklist, but rather as a matter of risk management.
“As we work with survivors, we should remember that every survivor is different and will likely have different safety needs because technology is constantly evolving,” said Shulruff.
There are several challenges to keep in mind when creating a safety plan for technology. Technology-facilitated abuse can often heighten a survivor’s fear of technology; something as simple as text messaging can cause apprehension if a survivor has experienced abuse via text messaging. This fear may be minimized unintentionally by others who are unfamiliar with the harm that technology-facilitated abuse can cause.
When creating a safety plan, it is a good idea to start out with questions in order to best tailor the plan to the survivor’s needs. It is important to stress that safe and private usage of technology is possible.
Learn more about technology safety – and find resources on stalking – at TechSafety.org.